A few weeks ago, one of our clients - a top-tier hedge fund – was concerned that they might become the target of a DDoS (Distributed Denial of Service) attack. Ahead of a scheduled transfer to an upgraded part of our platform that included automated DDoS mitigation software, we dropped everything and were able to protect them within 3 hours of getting the call!
As it turns out, they did get attacked and never went down (nor did any of our other clients). But without some quick thinking both by our client and our team, it would have turned out very badly. An attack like this would have compromised the trust of the hedge fund’s clients in an industry where trust, reliability, and confidentiality are crucial.
Here's a video that explains what DDoS is pretty well:
It's getting worse, not better.
Last week, an attack using the Internet of Things (smart appliances) took down a DNS platform used by many major sites. Basically, hundreds of thousands of cctv cameras, smart refrigerators, coffee makers, and toasters helped to bring down Spotify, Reddit, the New York Times, WIRED and many other sites. This is an alarming development because the "IoT" has not been scrutinized for security vulnerabilities the same way many other parts of the Internet have.
Here's a map of the outage:
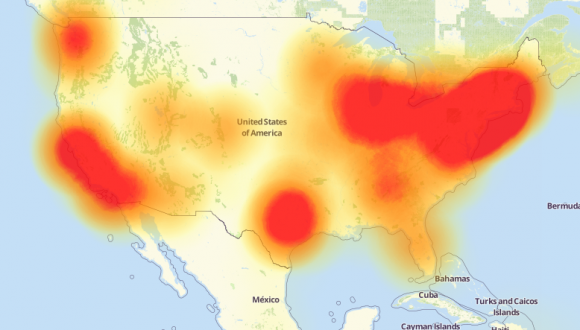
Credit: Downdetector.com
Afterward, President Barack Obama said that U.S. investigators "don't have any idea" who was behind the attack. On Jimmy Kimmel Live, he added that future presidents will face the challenge of "how do we continue to get all the benefits of being in cyberspace but protect our finances, protect our privacy. What is true is that we are all connected. We're all wired now."
So where do we go from here?
When someone can rent a service and launch an attack for $5/hour AND enlists toasters to help, it really changes the calculus. This is an arms race and it's an expensive one ($170 billion annually by 2020, with security on IoT expected to be 348 million in 2016). So expect costs to rise and more service outages. Sorry.
If your organization is not thinking security, they should be. At a minimum, get your website PEN tested (tell your developer/host first and do it off hours), make sure website administrators are not sharing their usernames and passwords, insist on stronger passwords, consider 2-step validation, chose hosts that have automated DDoS mitigation capabilities, choose web partners that know security matters and use latest best practices while developing and can keep scripts updated over time.
Here’s how we protected our Hedge Fund client. We spun up another compute node (virtual computer) in our private cloud to isolate it from everything else, migrated the website and database, tested it, debugged it, routed the site to a dedicated IP (to further isolate it) and coordinated DNS update with the client. Again, all said, from the first phone call to the last was about three hours.
Luckily, our client trusted us and called us in advance. That kind of trust is built over time and is strengthened when we respond quickly and effectively.
Good luck out there! It's the Wild West all over again and this time, billions are at stake. If you're unaware, we can help. If you are keenly aware, please drink in moderation, learn to meditate and give us a call when you need your website redone.
Be well,
- Todd
If you have any comments, questions or just want to say hi, please email me at todd.rengel@animusrex.com.
If you want to dig a bit deeper:
More reading on last week's IoT DDoS attack:
- https://dzone.com/articles/attack-of-the-internet-of-things
- https://www.wired.com/2016/10/internet-outage-ddos-dns-dyn/
- http://www.npr.org/2016/10/22/498954197/internet-outage-update-internet-of-things-hacking...
Additional Exploration on DDoS:
- https://www.akamai.com/us/en/our-thinking/state-of-the-internet-report/global-state-of-the-internet-security-ddos-attack-reports.jsp
- http://cybersec.buzz/ddos-attacks-continue-to-increase/
- http://www.zdnet.com/article/ddos-attacks-increase-over-125-percent-year-over-year/
- http://readwrite.com/2016/10/22/the-internet-of-things-was-used-in-fridays-ddos-attack-pl4/
- http://readwrite.com/2016/10/24/dyn-ddos-attack-sheds-new-light-on-the-growing-iot-problem-dl4/
- https://krebsonsecurity.com/2016/10/hacked-cameras-dvrs-powered-todays-massive-internet-outage/
- http://www.popularmechanics.com/technology/infrastructure/a23504/mirai-botnet-internet-of-things-ddos-attack/
- http://www.computerworld.com/article/3135285/security/ddos-attack-shows-dangers-of-iot-running-rampant.html